

Requirements
To implement this alternative approach, there are a few requirements that must be met:
- You must be deploying the container in a Kubernetes cluster.
- The application must support adding JVM parameters via an environment variable.
Starting Point
Let's assume that your application is using a StatefulSet that looks something like this:
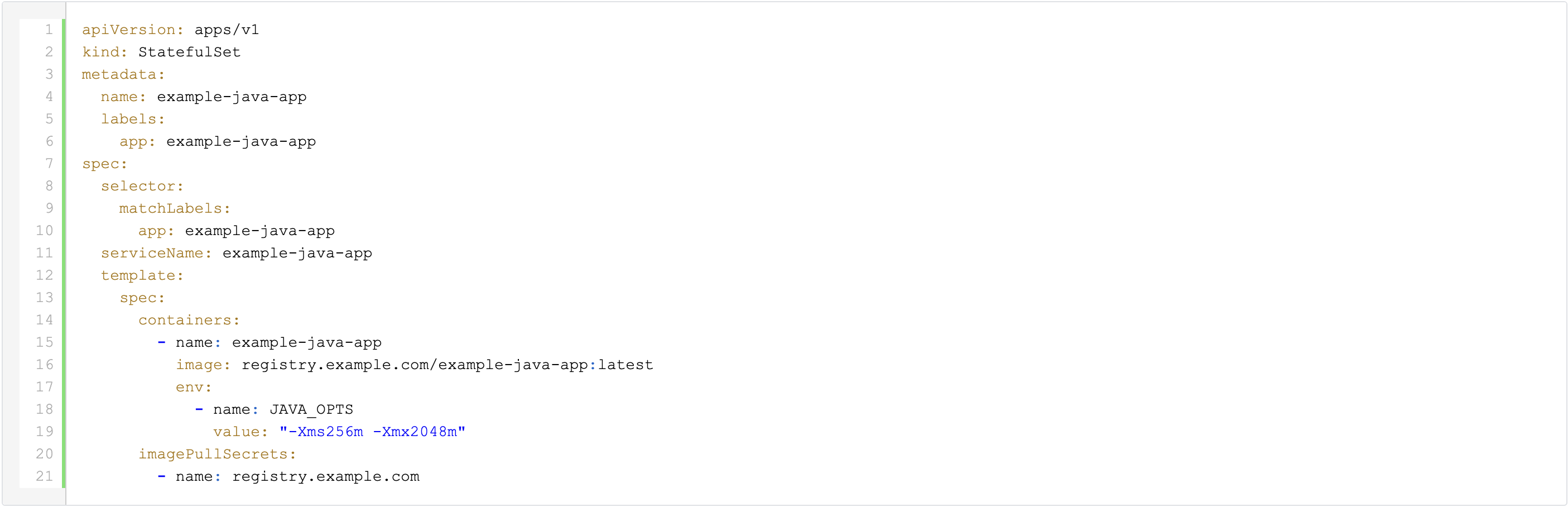
The name of the JAVA_OPTS environment variable may vary depending on the specific application.
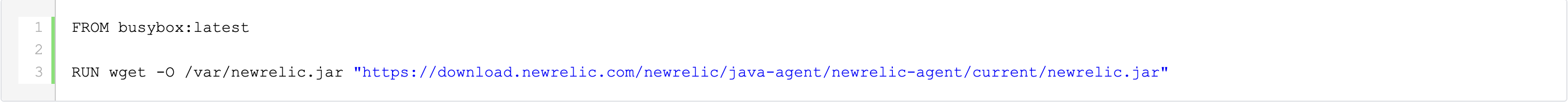
Packaging the New Relic agent jar
To simplify the deployment process, we will create a custom image which contains the New Relic agent jar. To create this image, we will use a Container File, which might look something like this:
"Injecting" the New Relic agent into the application container
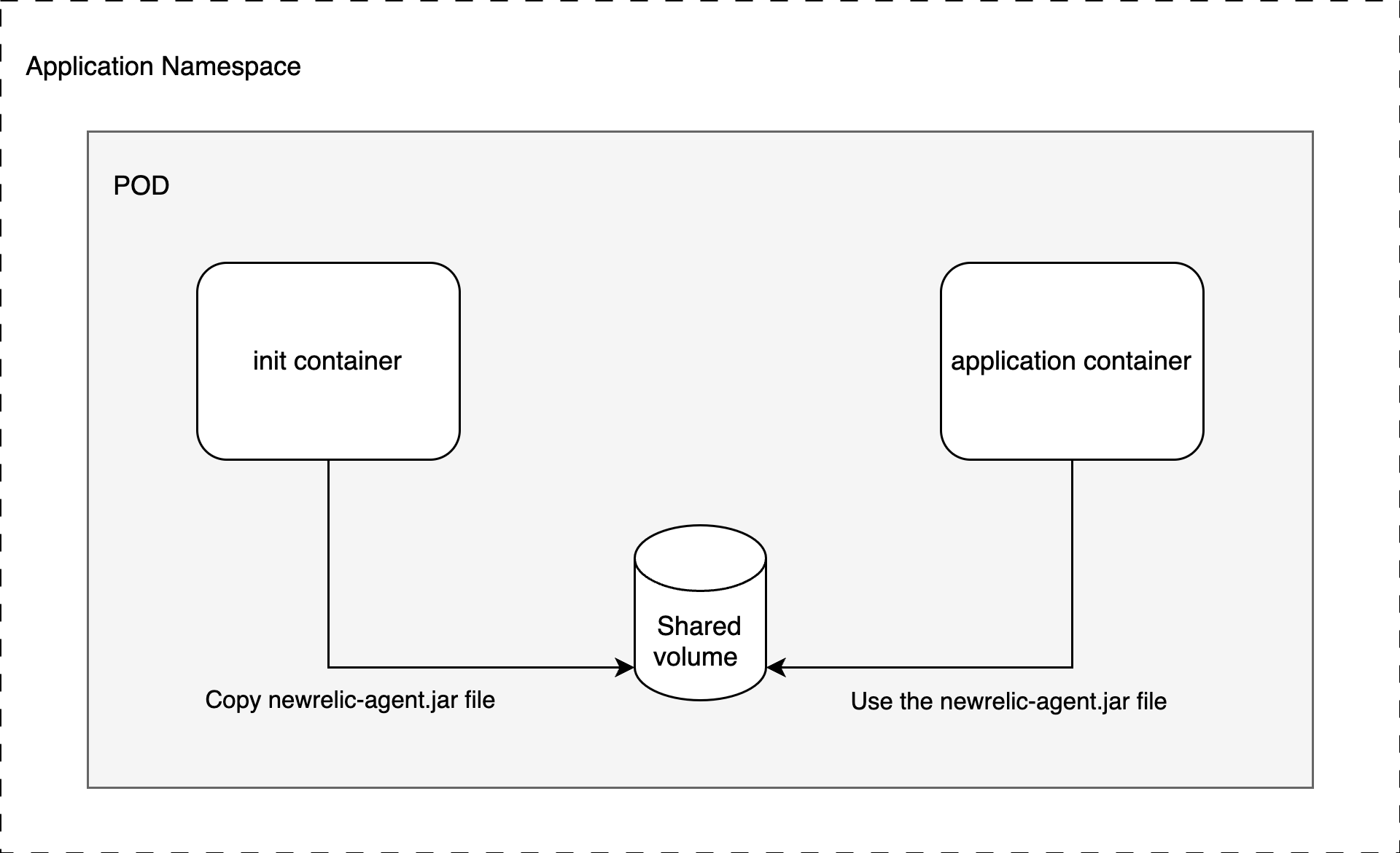
In order to direct the application to use the New Relic agent jar, we will utilize the Kubernetes Init Container and emptyDir concepts.
The resulting StatefulSet will look like this:
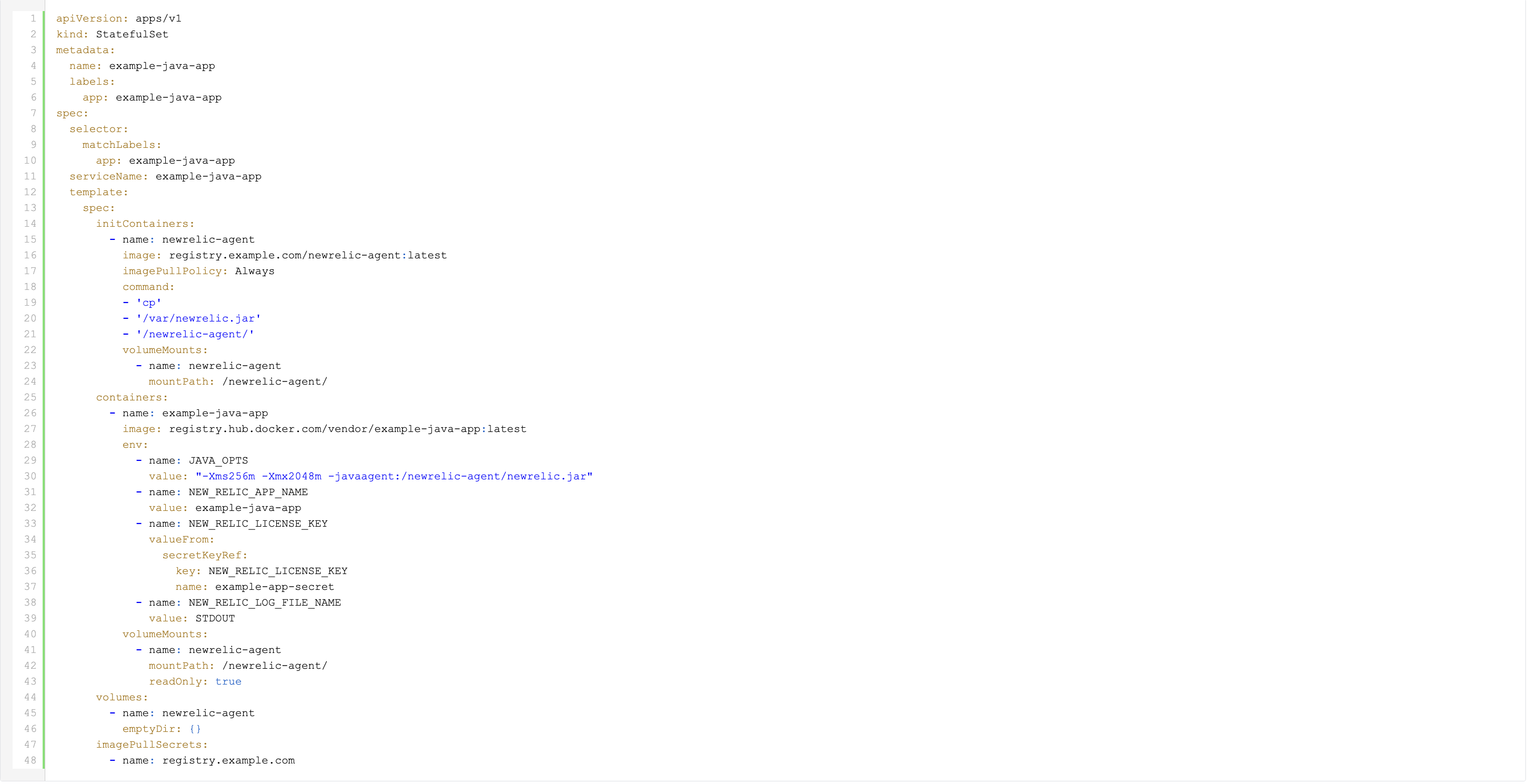
Instead of including the New Relic agent jar in the application image, we use our custom newrelic-agent image as an Init Container. This container copies the newrelic.jar file to an emptyDir volume.
Since the Init Container runs before the regular application container and both share the same volume, the newrelic.jar file is accessible when the JVM starts.
Apart from the shared volume, we need a few New Relic agent specific environment variables:
- NEW_RELIC_APP_NAME: to set the application name
- NEW_RELIC_LICENSE_KEY: to provide the license key
- NEW_RELIC_LOG_FILE_NAME: to optionally set a non-default log location, in this case STDOUT
There are a few additional environment variables available in the New Relic Java agent documentation that can be used.
In addition to this basic configuration, you can use the New Relic server-side agent configuration.
As you can see in the JAVA_OPTS environment variable, we still need to instruct the JVM to use the New Relic agent jar. It’s worth mentioning that this particular file is located on the shared volume.
Also note the "imagePullPolicy" which we have set to "Always" to ensure we always retrieve the latest image version even if it is still using the same tag.
Updating the New Relic agent
To ensure that the New Relic agent is always up-to-date, you can set up a Continuous Integration pipeline that automatically builds a new container image whenever a new agent version becomes available.
Additionally, you can tag the image with major, major.minor, and major.minor.patch, in addition to "latest". This allows you to pin the agent version based on the specific requirements of your application.
Depending on the image tag specified in the application's manifest file, updating could be as easy as restarting the application pods.
If you prefer to pin the New Relic agent to a specific version, you will need to update the newrelic-agent image tag in the StatefulSet and deploy this change to your Kubernetes cluster.
In any case, you no longer need to build a custom image just to add the New Relic agent jar, which should allow for more frequent updates to the agent.
Diagram
Do you want to discover more about Kubernetes?


What others have also read


In today's digital world, it's crucial to offer a smooth and personalized experience to your customers, no matter which channel they use to communicate with you. For this, Digital Experience Platforms (DXPs) are the solution. DXPs act as a central hu
Read more

CloudBrew has always been a highlight on our calendar, but the 2025 edition felt different. Perhaps it was the timing. Just the month prior, November 2025, the Azure Belgium Central region finally opened its doors. ACA has always operated from the he
Read more

Better uptime, lower costs, and avoiding vendor lock-in. These are three of the reasons why our customers opt for a multicloud strategy. Our Cloud Project Manager Roel Van Steenberghe explains what such a strategy entails and what the advantages of G
Read moreWant to dive deeper into this topic?
Get in touch with our experts today. They are happy to help!

Want to dive deeper into this topic?
Get in touch with our experts today. They are happy to help!

Want to dive deeper into this topic?
Get in touch with our experts today. They are happy to help!

Want to dive deeper into this topic?
Get in touch with our experts today. They are happy to help!

